Tracking Undercover DPRK IT Workers Through InfoStealer Logs
Uncovering Coordinated Multi-Identity Operations Through 1 Million Botnet Telemetry Records

Introduction: Limitations of Existing Methodologies
The infiltration of global remote IT markets by North Korean workers using fraudulent identities has become a persistent threat. The scale of this operation is well-documented in US Department of Justice indictments, FBI advisories, and international sanction lists.
Traditional security analyses have heavily relied on malware reverse engineering. However, disguised North Korean IT workers (hereafter DPRK operatives) rarely deploy malware directly. Instead, they integrate into standard development environments—committing code to GitHub, attending Slack meetings, and resolving Jira tickets. By perfectly mimicking the behavioral patterns of legitimate remote developers, they render signature-based detection mechanisms entirely ineffective.
This research took a different starting point. It analyzed infection logs of InfoStealer malware from the deep and dark web as its primary source. When the devices used by these operatives were themselves compromised by InfoStealers, they inadvertently leaked critical telemetry: email credentials, passwords, access IPs, and unique hardware IDs. And these traces provided the foundational intelligence necessary to reverse-trace and map the operatives’ underlying operational infrastructure.
Table of content
- Methodology: Cross-Validation of Common Indicators
- Key Findings
- Five Personas Operated From a Single Device
- Korean Language Keyboards Reveals Identity
- Password Pattern Clustering Identifies Distinct Operational Groups
- Three-pronged Infrastructure Set — SMS Proxy Services, VPN, and Remote Access
- Russian ISP TransTeleCom Identified as Core Infrastructure
- Operational Group Profile
- Key Artifact Analysis
- Conclusion
Methodology: Cross-Validation of Common Indicators
The analysis established a baseline using 1,879 DPRK operative-related email account patterns previously disclosed by the US government and private research institutions. We then cross-referenced this baseline against 1,045,645 InfoStealer infection records collected from the deep web since 2024.

Figure 1. Distribution and density of entire telemetry data set
The starting point of this analysis was to verify whether more than one million telemetry records could be interpreted through clustering. Visualization based on key botnet infection data—such as email addresses, IP addresses, and passwords—led to the conclusion that this data can serve as an analytical indicator representing the activities of DPRK operative groups. These validated data clusters form the foundation of the findings presented in this report.
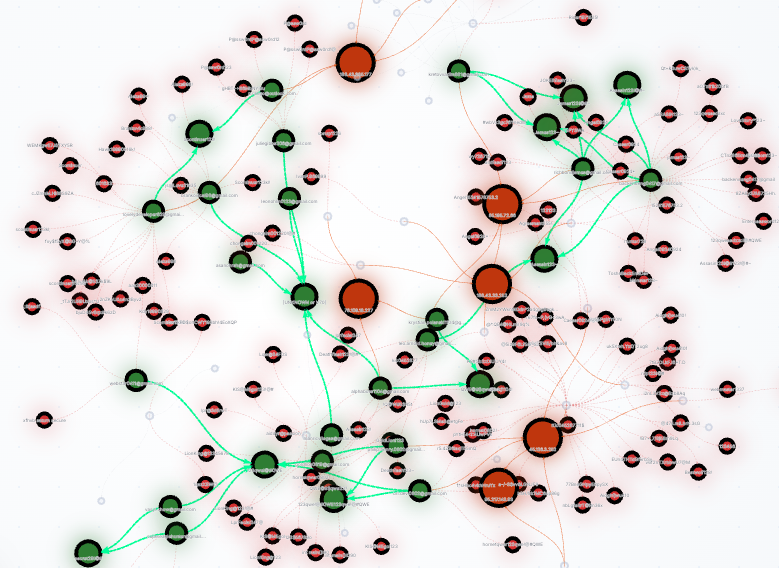
Figure 2. Password similarity clustering using the Levenshtein algorithm
o visualize the data leaked through botnet infections, the analysis extracted key indicators, such as email accounts, IP addresses, passwords, and shared passwords. To quantify password similarity, we applied the Levenshtein Edit Distance algorithm to visualize these data. Cross-referencing these clusters against established DPRK IT worker TTPs allowed us to isolate high-confidence groups. All findings presented in this report underwent this cross-validation process.
| Key Indicator | Analytical Approach |
|---|---|
| Email Account | Primary pivot for account correlation; domain and local-part pattern analysis |
| IP Address | Shared IP, C-Class subnet, and ASN infrastructure mapping |
| Hardware ID | Multi-account detection on shared devices |
| Password | Password family clustering using the Levenshtein algorithm |
Table 1. Classification of key telemetry data
To evaluate the validity of the correlated telemetry, we established a three-tier confidence model.
| Confidence Level | Criteria |
|---|---|
| High | Match across three distinct indicators (IP address, password, and Hardware ID) |
| Medium | Match across two independent indicators, or a single high-fidelity indicator. |
| Low | A single low-fidelity indicator (e.g., shared C-Class subnet or common password). |
Table 2. Confidence level and criteria
The analysis identified 80 unique email accounts, 66 IP addresses, and 66 hardware IDs, all of which were associated with 490 domains across 28 countries.
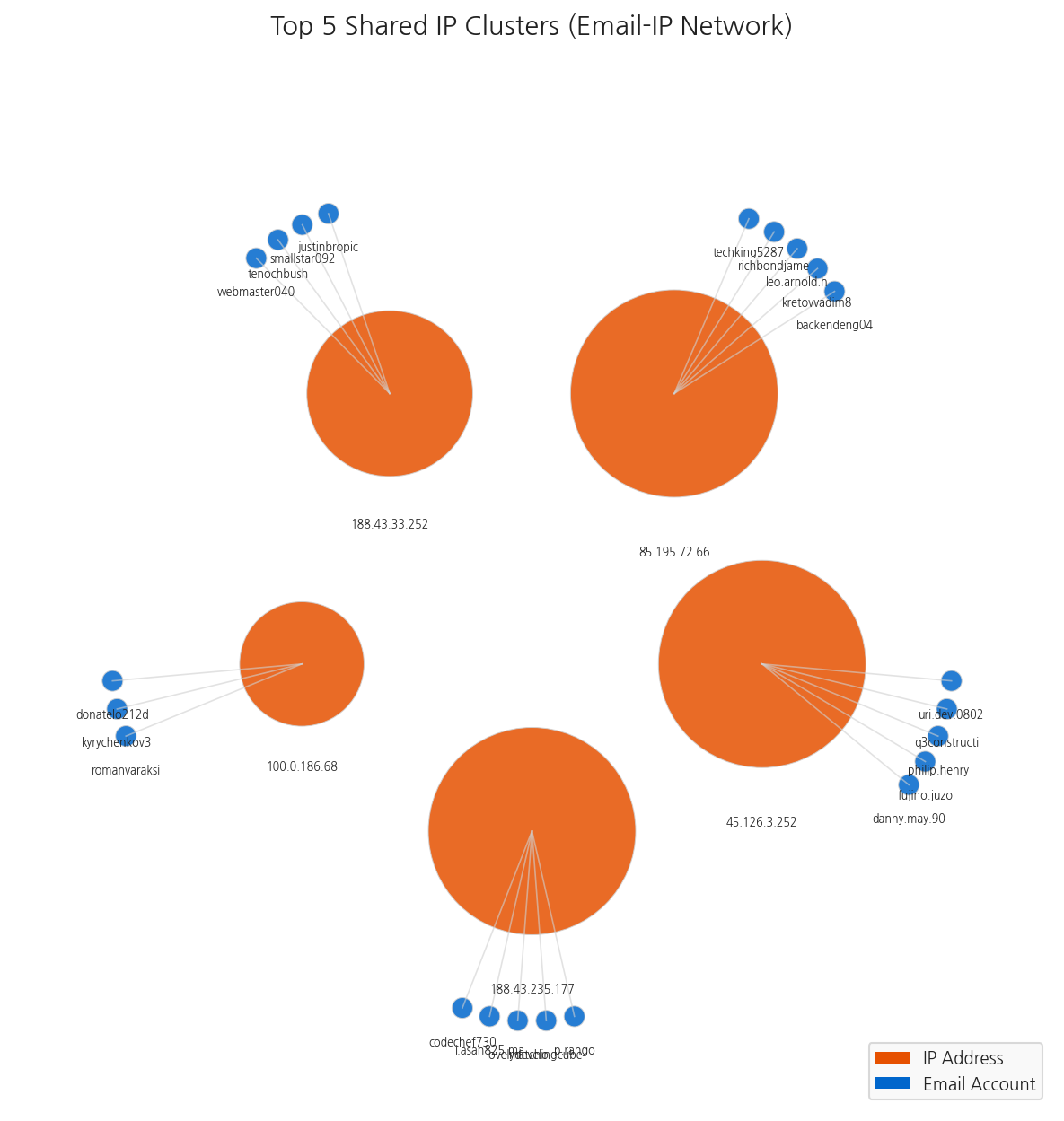
Key Finding 1: Five Personas Operated From a Single Device
The most notable finding emerged from hardware ID clustering, revealing up to five email accounts tied to a single physical device. (Note: The majority of the accounts analyzed in this report are Gmail. Throughout this report, any email address listed without a domain implies a @gmail.com suffix.)
| Hardware ID (partial) | Number of Related Email Accounts | Email Accounts |
|---|---|---|
65BSLIZSLNT8XOE0NMM | 5 | backendeng0417, kretovvadim881, leo.arnold.honey, richbondjames, techking5287 |
88B59F2CF1ACE41FCB4E | 5 | codechef730, i.asan825.mail, lovelydeveloper829, matchingcube, p.rango |
2WU1NIB0KVZFV9YJG19 | 4 | justinbropico, smallstar0924, tenochbush, webmaster0407 |
Table 3. Persona distribution per hardware ID
These findings indicate that operatives go beyond simple device sharing; they concurrently manage multiple fraudulent personas and freelance profiles from a single endpoint. This operational setup enables parallel employment campaigns. For instance, from the same device, an operative can apply for a backend engineering role under the persona 'backendeng0417' while actively targeting another organization under the persona 'richbondjames'.
Key Finding 2: Korean Language Keyboards Reveals Identity
Mismatches between personas and underlying system language configurations provide compelling evidence for identifying the group behind the operation.
| Email Account | Username/Profile | Country of Access | OS Language Settings |
|---|---|---|---|
fujino.juzo@gmail.com | Japanese | Finland, Hong Kong | English (US), Korean (Korea) |
felix44291@gmail.com | Western-sounding name | USA, Japan | English (US), Korean (Korea) |
Table 4. Discrepancies between persona nationality and system language configurations
In the first case, analysis confirmed that despite using a Japanese name, the device was configured with a Korean keyboard. This strongly indicates that the actual user is a native Korean speaker, not Japanese.
InfoStealer logs capture the OS language and keyboard settings of infected devices. While threat actors can easily fabricate personas, underlying device language configurations are frequently overlooked.
Key Finding 3: Password Pattern Clustering Identifies Distinct Operational Groups
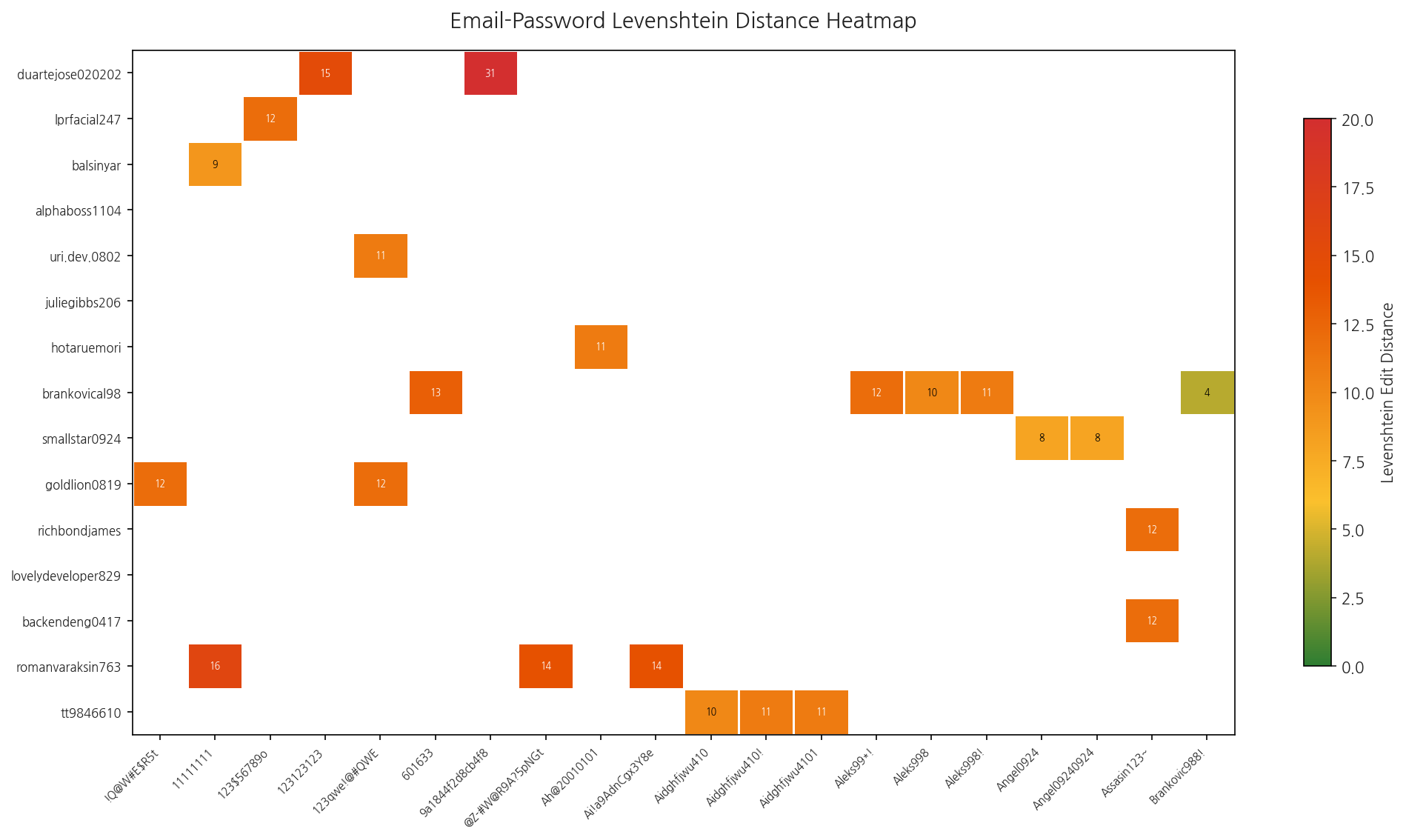
Figure 3. Visualization of password patterns within the collected telemetry
Analysis revealed that specific passwords were reused across multiple email accounts, despite those accounts claiming different nationalities and names. The use of identical passwords by accounts presenting distinct identities serves as a key indicator that these are not independent freelancers, but members of a single, coordinated operational group.
Xiah@1998123: This password was used identically across four email accounts (balsinyar,duartejose020202,kyrychenkov30,romanvaraksin763).123qwe!@#QWE: Shared across six email accounts, this string exhibits a "keyboard-walk" pattern—typing characters sequentially based on keyboard layout. This specific pattern has been repeatedly observed in North Korea-linked operations.
Furthermore, clustering via the Levenshtein algorithm confirmed that these operatives followed systematic modification rules rather than relying solely on simple reuse:
- Assasin Family:
Assasin123!→Assasin123~→Assasom123~→aSSASIN123~ - James Family:
James123~→james123~(shared across 3 email accounts) - Email Derivation Pattern: Deriving the password directly from the local part of the email address (e.g., Email:
lprfacial247@gmail.com→ Password:lprfacial247).
These "convenient passwords", chosen by operatives managing large-scale accounts for ease of recall, paradoxically have become decisive clues enabling security analysts to identify and track threat actors.
Key Finding 4: Three-pronged Infrastructure Set — SMS Proxy Services, VPN, and Remote Access
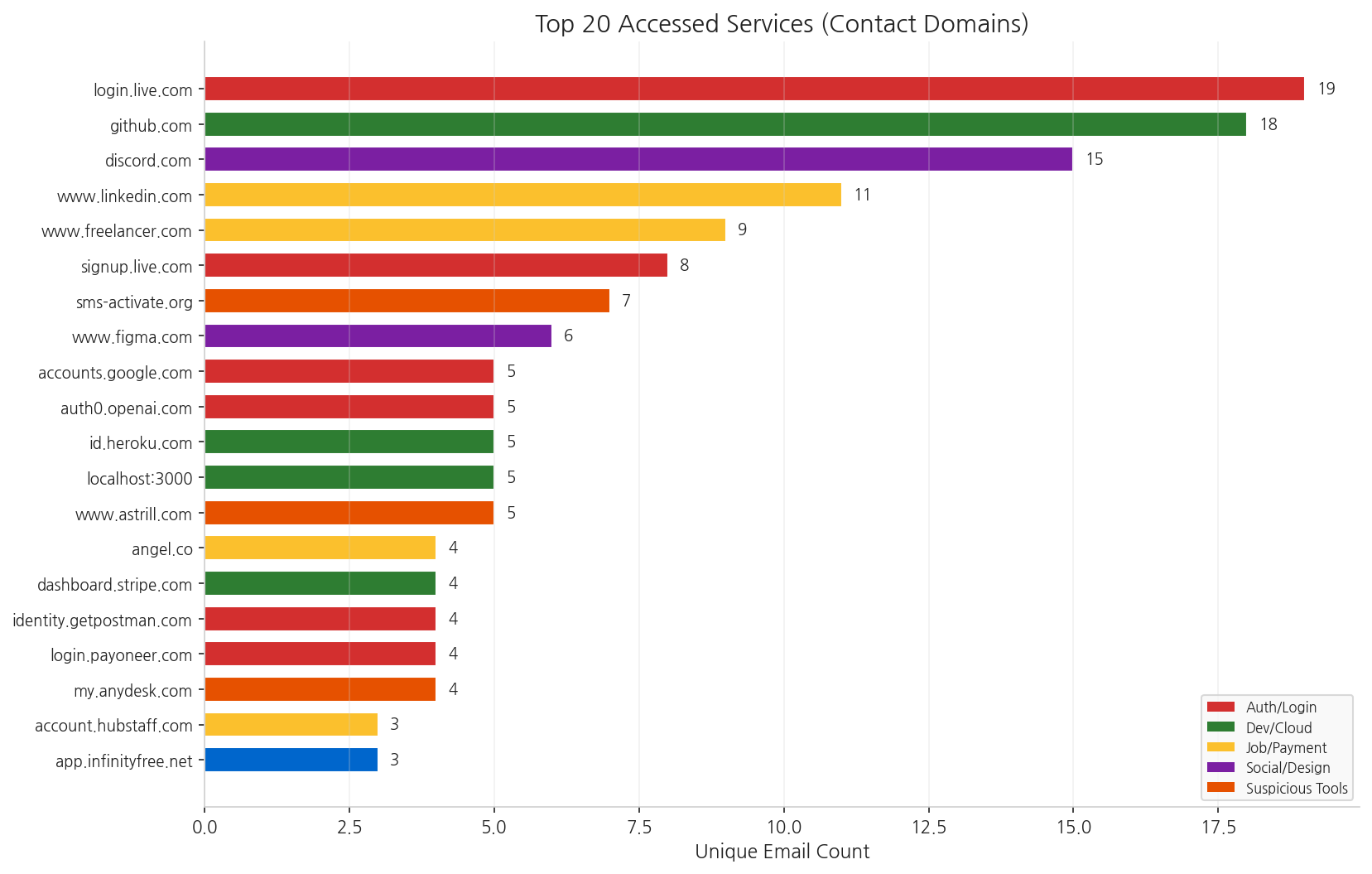
Figure 4. Analysis of accessed domain services
The list of services accessed by email accounts reveals the full picture of the DPRK operative infrastructure.
| Service | Number of Email Accounts Accessed | Operational Role |
|---|---|---|
sms-activate.org | 7 | SMS proxy service for renting verification numbers to create fake accounts. |
www.astrill.com | 5 | VPN service frequently favored by DPRK operatives. |
my.anydesk.com | 4 | Remote desktop — used for proxy access or remote control of shared machines. |
Table 5. Key services accessed by DPRK operatives to conceal their identity
At the same time, these accounts were actively operating across multiple services to appear as legitimate freelancers.
| Platform | Number of Email Accounts Accessed | Use Case (Purpose) |
|---|---|---|
github.com | 18 | Code portfolio management and commits |
www.linkedin.com | 11 | Job search |
www.freelancer.com | 9 | Securing freelance contracts |
angel.co | 4 | Applying for startup roles |
login.payoneer.com | 4 | Payment collection |
dashboard.stripe.com | 4 | Payment collection |
Table 6. Legitimate platforms exploited for freelance persona cultivation
Through the domain access logs of these DPRK operatives, we identified a highly systematic operational pattern:
Job Application → Payment Collection → Location Obfuscation (VPN) → Account Verification Bypass (SMS Proxy)
This report assesses this specific sequence as the primary operational lifecycle driving the employment campaigns of DPRK operatives.
Key Finding 5: Russian ISP TransTeleCom Identified as Core Infrastructure
An ASN analysis of the 66 extracted IP addresses revealed a significant concentration within a specific Russian telecommunications provider.
AS20485 Joint Stock Company TransTeleCom (Russia): 7 IP addresses, 11 associated email accounts
TransTeleCom is a major backbone telecommunications provider in Russia. This high concentration within a single ASN strongly suggests a reliance on Russian hosting or its deployment as a VPN exit node.
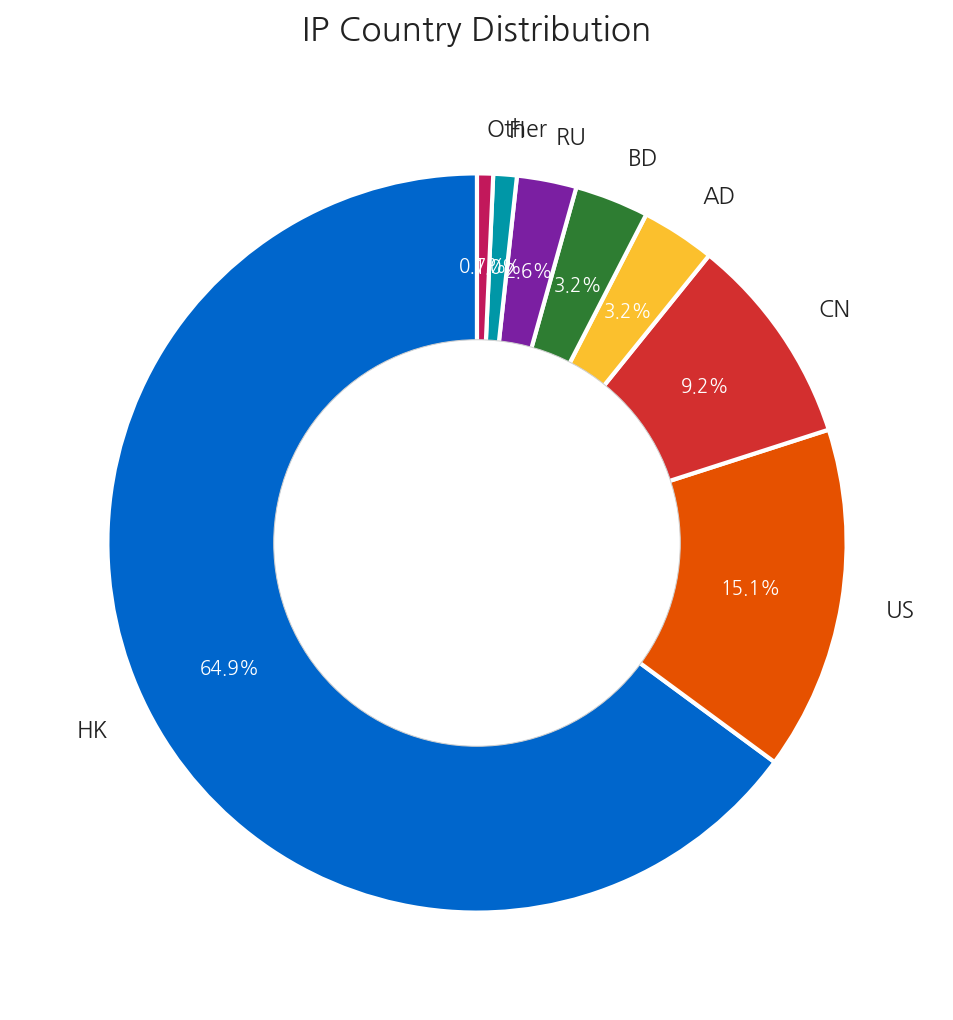
Geographically, Hong Kong accounted for 64.9% of all events. Major domestic and international intelligence agencies, alongside prior security reports, have already identified Hong Kong as a key hub utilized by DPRK IT workers; our findings fully align with these existing threat assessments. Furthermore, this indicates that operatives are likely leveraging VPN services based in Hong Kong to conceal their true geographic locations.
Operational Group Profile
This summarizes the characteristics of the five operational groups identified.
Group 1 — Germany-based, five personas tied to a single device
- HWID:
65BSLIZSLNT8XOE0NMM - Email Accounts: backendeng0417, kretovvadim881, leo.arnold.honey, richbondjames, techking5287
- Notable feature: Highest incidence of password reuse (shared within the James/Assasin family)
Group 2 — Russia-based, unified language configurations
- HWID:
88B59F2CF1ACE41FCB4E - Email Accounts: codechef730, i.asan825.mail, lovelydeveloper829, matchingcube, p.rango
- Notable feature: All accounts uniformly set to English (United States), indicating deliberate configuration management.
Group 3 — Russia-based, absence of language settings
- HWID:
2WU1NIB0KVZFV9YJG19 - Email Accounts: justinbropico, smallstar0924, tenochbush, webmaster0407
- Notable feature: Absence of language setting information
Group 4 — Multi-national operation, Highest confidence cluster
- HWID:
20A1F78D427D13056976and others - Email Accounts: balsinyar, duartejose020202, romanvaraksin763 (linked to + kyrychenkov30)
- Notable feature: Accessed from 6 countries while sharing the exact password
Xiah@1998123. This provides significant evidence of a highly interconnected operator network.
Group 5 — Russia-based, developer-specific nicknames
- HWID:
22EAD21274BD7FBDA6B6 - Email Accounts: codechef730, codewarrier3000, svendev128
- Notable feature: Usernames are explicitly tailored for developer roles (codechef, codewarrier), demonstrating a focused targeting of technical employment opportunities.
Key Artifact Analysis
Email Accounts (High Confidence)
The following is a list of email accounts associated with DPRK operatives, identified through various threat indicators. Notably, a single email account exhibiting complex correlations with up to 8 IP addresses, 2 passwords, and 8 Hardware IDs represents a highly anomalous pattern that deviates significantly from legitimate user behavior.
The “1:N” multi-mapping pattern provides strong evidence that these accounts are not operated by individual users but are instead centrally managed as part of a coordinated fraudulent identity infrastructure.
kyrychenkov30@gmail.com (IP×8, PW×2, HWID×8)
romanvaraksin763@gmail.com (IP×6, PW×3, HWID×6)
balsinyar@gmail.com (IP×6, PW×2, HWID×6)
backendeng0417@gmail.com (IP×1, PW×4, HWID×1)
richbondjames@gmail.com (IP×1, PW×4, HWID×1)
ASN/IP
Password Patterns
Registering the following patterns with credential monitoring or dark web leak detection systems enables the proactive detection of new email accounts belonging to the same DPRK operative group.
123qwe!@#QWE # 6 email accounts shared, keyboard-walk pattern
Xiah@[0-9]{7} # 4 email accounts shared, same operational group signal
Assasin123[~!@#]+ # Family cluster, suffix variation
James123[~!@#]+ # Family cluster, suffix variation
Geographical/Linguistic Anomalies
We strongly advise incorporating the following anomaly detection logic into recruitment platforms and corporate HR systems:
- Profile-System Language Mismatch: Trigger an alert when an applicant's claimed nationality or name conflicts with the OS or browser language settings of their accessing device.
- Abnormal Multi-Country Access: Flag accounts that log in from IP addresses spanning three or more countries within a compressed timeframe (e.g., 7 days).
- Single-Device Multi-Account Access (Duplicate HWID): Generate immediate alerts when multiple jobseeker profiles access the platform from the exact same Hardware ID. (Implementing session or browser fingerprinting on the recruitment platform is highly recommended).
- Virtual Number Authentication: Flag accounts verified using phone numbers issued by services such as sms-activate.org.
Recruitment Process Recommendations
To effectively block infiltration by DPRK operatives, we recommend implementing the following multi-layered security controls throughout the recruitment lifecycle:
- Verification — Multi-Dimensional Identity Vetting: Cross-check the authenticity of the applicant's LinkedIn profile, professional activity, and GitHub commit history. During video interviews, mandate the use of deepfake detection tools to confirm the applicant's true physical identity.
- Identification — Behavioral Red Flags: Exercise heightened caution regarding candidates who insist on using specific cross-border payment platforms (e.g., Payoneer, Wise) prior to contract signing, or those who request the routing of internal access OTPs to public SMS numbers.
- Control — Endpoint and Infrastructure Monitoring: Whenever feasible, provision dedicated corporate devices to remote workers and enforce Mobile Device Management (MDM) solutions. This facilitates the continuous monitoring of access IPs and ASNs, enabling the real-time detection of anomalous access.
Conclusion
This report reveals two key findings.
First, DPRK operatives disguised as IT professionals do not represent mere individual-level fraudulent activity; rather, they are part of an organized operation utilizing a highly coordinated "multi-identity infrastructure." The simultaneous management of five or more personas from a single device, the systematic modification of passwords, and the combination of SMS authentication proxies with VPNs clearly demonstrate that these actors belong to a thoroughly trained organization.
Second, this research demonstrates that InfoStealer telemetry can be effectively leveraged to track such evasive groups. Traditional malware reverse engineering methods face significant limitations when tracking organizations that do not distribute malware themselves. However, the paradoxical reality that even threat actors can become infected with malware provides a critical new lead for tracking. Minor traces left in botnet logs—such as hardware IDs, language settings, and reused passwords—become the most decisive clues to pierce through false personas and reveal the true operators. As seen in cases where falsified Japanese identities were exposed by the use of Korean keyboard settings, decisive intelligence often emerges from the most trivial operational security failures.
The infiltration of overseas organizations by DPRK operatives is not merely a means of generating foreign currency. The internal system access rights, source code repositories, and cloud console credentials they secure can easily become initial access vectors for larger, destructive cyberattacks. Ultimately, proactively detecting these disguised operatives at the recruitment stage remains the most economical and robust line of defense for comprehensive corporate risk management.