Contents Download
1. Cybersecurity Issues: May 2024
In this issue of the Logpresso CTI Monthly Report, Chapter 1 covers notable cybersecurity issues that occurred last May. It also includes recommendations for preventing these threats.
- Hacking of the Social Media Account belonging to the French Minister of Sports
- Increase in Cyberattacks Infiltrating Corporate Networks Networks Through VPNs
- Various Malware Distributed Through Pirated Office Software
- Hacking of ‘Sungsimdang’ Online Shopping Mall
- A Phishing Attack Using Fake ‘DocuSign’ Templates
2. Threat Analysis
The recent Logpresso CTI Monthly Report addresses the surge in credential leak incidents in Asian countries. The June issue analyzes cases in India, following the previous issues’ focus on Japan and Taiwan.
- Credential Leak Due to Malicious Bot Infections in India
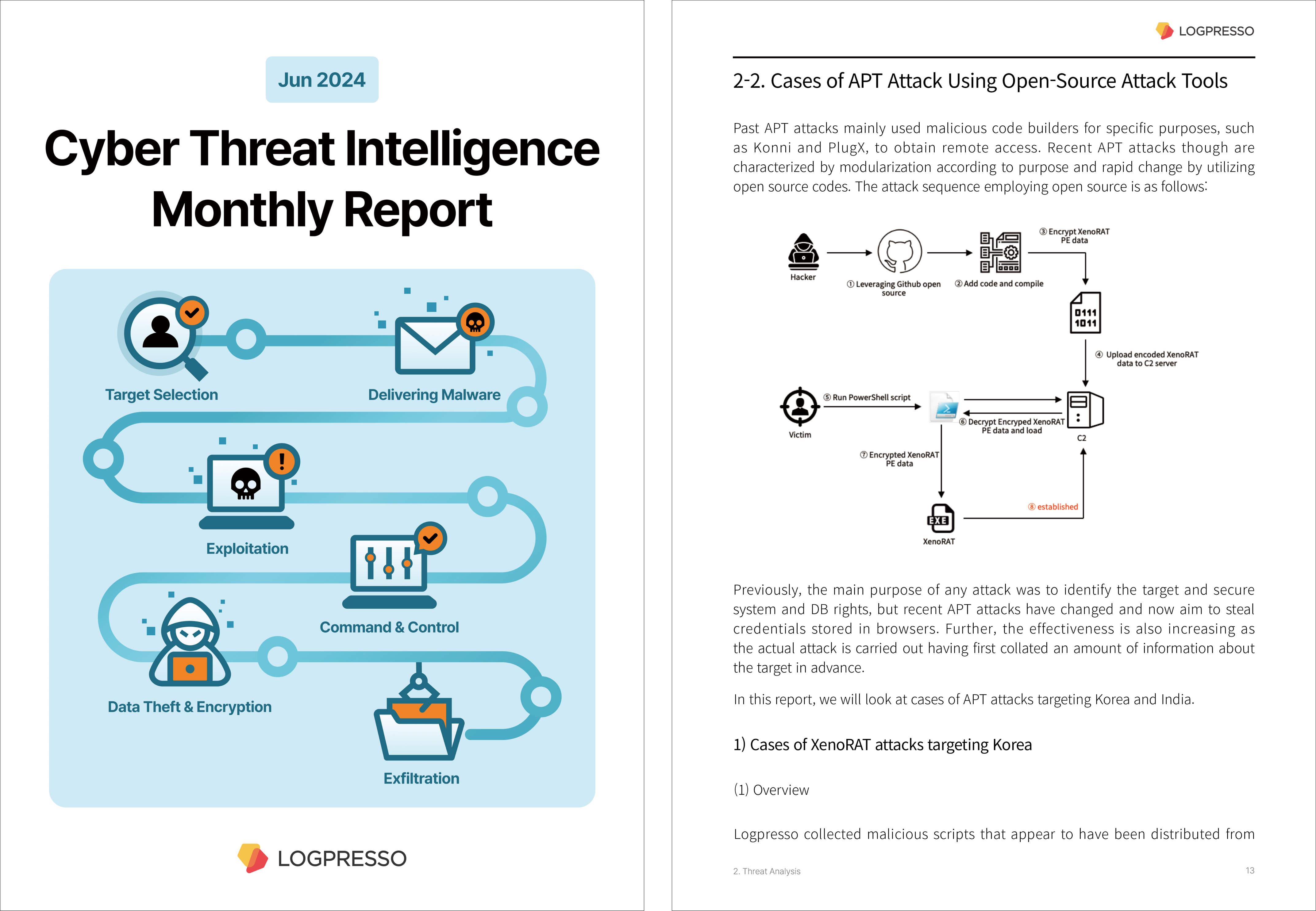
- Cases of APT Attack Using Open-Source Attack Tools
Contents Download

Logpresso Cyber Threat Intelligence
Logpresso is a specialized company in security and IT operations(SecOps), established in 2013. We offer security operation solutions such as log management, SIEM(Security Information and Event Management), SOAR(Security Orchestration, Automation, and Response), and DFIR(Digital Forensic & Incident Response) based on our fundamental technology.
Logpresso CTI is a cyber threat intelligence service optimized to immediately utilize such security threat information in security information and event management (SIEM) / security orchestration, automation, and response (SOAR) platforms. Relying on various open-source intelligence (OSINT) data sources such as the dark web and deep web, Logpresso CTI provides intelligence feeds that can detect various cyber-attacks including advanced persistent threats (APT), phishing, and credential stuffing.
Unlike many CTI services that are only available on a limited basis through API, Logpresso CTI synchronizes all indicators of compromise (IoC) directly to SIEM/SOAR, enabling full, real-time investigation of all logs. Unlike existing security architectures that primarily rely on detection through security devices, our approach enables the detection of threats proactively before a direct attack occurs.



